
Table of Contents (6 sections)
Behind a trashmail is above all the approach not to give away one’s own e-mail address. This protects against spam & phishing mails. Because all too often it is already suspected during registration: If I enter my real e-mail address here, I will be spammed! We introduce three providers. The Trashmail providers should be used with caution!
Why should I use a Trashmail provider?
Spam and phishing mails are a big problem. With new mailboxes there is calm at the beginning. But as soon as the first unsolicited e-mails start fluttering in, the others are not long in coming. And even if only an incredibly small percentage clicks on these e-mails - they are clicked on. And that is exactly what the criminals are all about. At the end of the day, the e-mails are still very annoying. But if you share your e-mail address in forums and post on social networks, you should be prepared for more contact by e-mail.
Wherever it is simply a matter of proving that access to a mailbox exists, it is worth taking a look at the numerous trashmail providers. Usually, when you call up the website, a mailbox is displayed. This mailbox, with individual address, can now be specified on the website. The link, which is sent from the website for confirmation, will now be sent to the trashmail provider in the mailbox.
The link in the mail can now be clicked for confirmation. Especially for applications where it is clear beforehand that the visit to the website will only take place once, the use of trash mails is extremely worthwhile. However, if you forget your password after a few days, you will have a big problem. Because often you do not have access to the “throwaway” mailbox for days.
10 minute mail - if the mailbox does not exist for a quarter of an hour
The name says it all. As soon as the website is accessed, you will receive a mailbox. With the call of the website there is also a countdown. After 10 minutes it ends - if the counter is not reset. Nothing for eternity. But this function is actually quite practical. Because after 10 minutes nobody else can retrieve the e-mail either. That is the difference to other providers. If you know the e-mail, it can be partly retrieved by anyone.
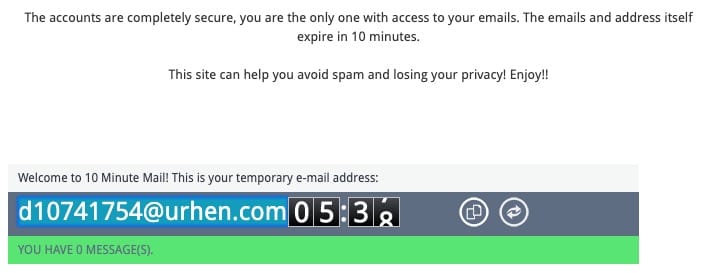
For 10 minutes the mailboxes of 10Minutemail exist. (Source:10minutemail.com)
Mail 1A - Create, retrieve and throw away mailboxes!
The Trashmail provider Mail 1A has a very tidy interface. There it becomes quickly clear what is necessary to do. But the upper left area is the most interesting. All trashmails have the domain “mail1a.de”, but here you can assign one-time email addresses as you wish. If you can remember the domain, you can also retrieve the e-mail recurrently. A difference to 10 minute mail!

Mail1A is characterized by a tidy surface. (Source: Mail1a.de)
Fake Mail Generator - easy use with multiple domains!
When calling the website of Fake Mail Generator, a disposable mailbox is immediately created. The rotating circle symbolizes waiting for e-mails. Since trash mails from websites are rather unpopular e-mail providers, it is good if several domains can be selected. This is possible with the Fake Mail Generator.
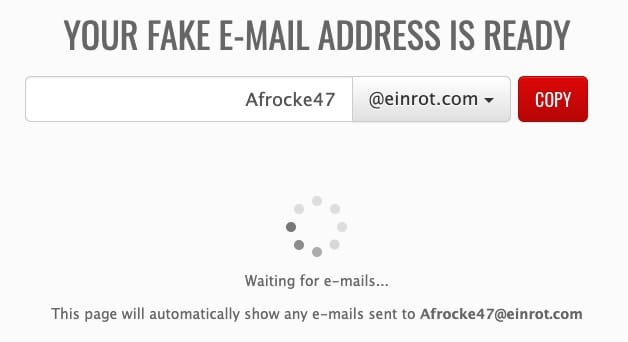
Several domains and you can start immediately - with Fake Mail Generator. (Source: fakemailgenerator.com)
You should not use Trashmail providers for this purpose!
You want to add a link on a website and are asked to register? A prime example for the use of a trashmail provider. But there are sites where the use is rather unsuitable. For the following websites you should refrain from using a disposable email:
-
- E-Mail provider
Cloud Storage
You should really only use a trashmail provider if you are sure that you don’t want or need another one after the first access. Since the e-mails are not encrypted and enjoy a generally low level of IT security, you should not be able to be inferred from this e-mail.
Alternative to Trashmail. Set up an alias for the mailbox!
If you don’t want to give away your e-mail address, but still want to receive e-mail in the long term, you should think about an alias. A second e-mail address in the same mailbox. Some e-mail providers offer this service. An e-mail alias may look like a separate e-mail address from the outside - but if someone sends an e-mail there, it will end up with another e-mail. This function is quite powerful. With some providers, however, this is only possible with a paid subscription. If the free version provides this function, then only to a very limited extent. If you have your own e-mail account, you can use as many aliases as you like. For providers of GMX there is a explanation.
Next Step
Our certified security experts will advise you on the topics covered in this article — free and without obligation.
Free · 30 minutes · No obligation
