
TL;DR
A Samsung NC10 laptop deliberately infected with six destructive malware strains - BlackEnergy, ILOVEYOU, MyDoom, SoBig, WannaCry, and DarkTequila - was sold as artwork titled The Persistence of Chaos for $1,345,000. Together these six strains caused an estimated $95 billion in global damages. The artwork by Guo O Dong is air-gapped and viewable via webcam, intended to make the real danger of malware tangible.
Table of Contents (2 sections)
It is an extraordinary auction - and probably the most expensive virus catapult in the world. The artwork called “The Persistence of Chaos” is a laptop infected with a wide variety of malware that has now been auctioned off for more than a million USD.
Virus slingshot comes under the hammer - viruses as art!
Virus protection programs, awareness training and other protection mechanisms such as firewalls and intrusion detection systems are all designed to help prevent malware from being captured. But this is not the case with the laptop that has now come under the hammer. The “work of art” bears the appropriate name “The Persistence of Chaos” and is completely unusable. The Samsung NC10 netbook has long been infected by encryption Trojans. But productive use is no longer the issue. But this is nothing new with art. But you can have a look at the spectacle. There are six malware programs on display. The auction sum is naturally high with over one million USD for such a laptop. But the damage caused by the installed malware is even higher. Together, these have caused damage of USD 95 billion worldwide. And these are the pests:
-
- BlackEnergy was responsible, among other things, for the power outage in Ukraine in 2015. But not exclusively. In general, this malware was used more frequently against Ukraine
- DarkTequila you don’t necessarily know it here in the country. The main target of the malware is Mexican users. Financial and company data
are interesting for the malware.
- ILOVEYOU is already a dinosaur under the malware. Since the year 2000, the software has been spreading via e-mail and writing “ILOVEYOU” in the subject line. Worldwide more than 500,000 networks have been disabled as a result
- MyDoom could be described as a precursor of Emotet. Email contacts have been written to, attachments have been sent. A damage in the amount of 38 billion USD goes alone on the account of this Malware
- SoBig has a similar dissemination strategy: e-mails. This malware even damaged hardware and secured its place on the artificial laptop. SoBig is responsible for 37 billion USD in damage, which is a credit to the name. And last but not least:
- WannaCry most people might still be familiar with. Even if the damage “only” amounts to four billion USD - in the news it has made it into the malware. The Encryption Trojan has attacked 200,000 computers in 150 countries.
Why and who takes the trouble to create a virus slingshot?
The work of art is intended to make the danger posed by malware tangible. For this reason, the artist duo “Guo O Dong” has registered the appropriate domain “The Persistence of Chaos”. There, thanks to a webcam, anyone can watch what happens on the laptop. 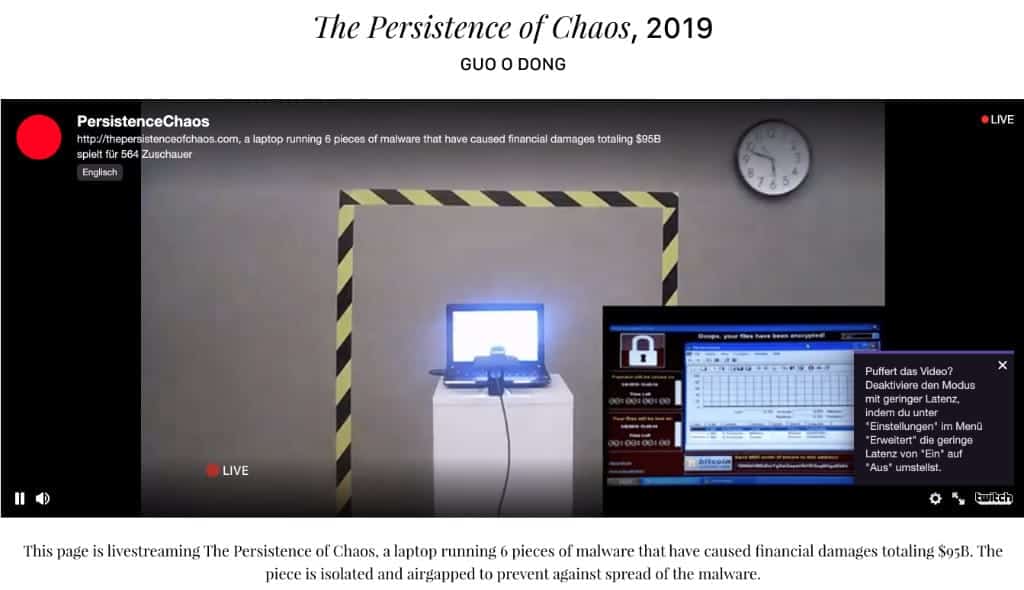
](https://thepersistenceofchaos.com/) The most expensive virus slingshot in the world - The Persistence of Chaos. Source: thepersistenceofchaos.com That, as already written, is not too much. A blocking tape symbolically protects other computers and networks from infection. It goes without saying that the computer is not connected anywhere. If you want to call such a virus slingshot your own, you have to infect your laptop yourself. The laptop was successfully auctioned for 1,345,000 USD.
Next Step
Our certified security experts will advise you on the topics covered in this article — free and without obligation.
Free · 30 minutes · No obligation
