
TL;DR
AWARE7's live hacking shows cover password cracking (dictionary attacks, personalized wordlists), social network reconnaissance, Call ID spoofing using forged police phone numbers, drone hacking, SMS spoofing, and crafted phishing emails. The goal is not to create fear but to empower audiences with practical protective measures. Dating back to 2006, the format emphasizes realistic demonstrations over staged scenarios, with audience interaction a central element.
Table of Contents (4 sections)
Different live hacking examples can make the danger of digitalisation tangible. But the goal is not to make people afraid of the future. At the end of every live hacking show it should be about recognizing and avoiding dangers. Too often we hear about successful scams that should be known.
The classic of the Live Hacking examples: Cracking the password.
The lecture history of the live hacking shows of the AWARE7 GmbH, respectively the former Institute for Internet Security, goes back to 2006. A lot has changed so far - but one thing has remained: Insecure passwords. In the classic user area, different live demonstrations, such as guessing a password in different ways, are a good live example to see with your own eyes how fast passwords can be guessed. On and offline attacks on protected files and accounts can be discussed in detail. But also the attack patterns in this area have changed over time. For example, dictionaries or pure coincidence are no longer valued. Information about a personal is valuable and is used to create personal password lists. This can also be shown very well in a live hacking. A password, however, its security is also not visible. Protective measures and recommendations on how a secure password can be thought up and managed belong in our view in every show in which it is shown how insecure passwords can be. We present foreign and own IT-Security projects, which are an ad-free help for self-help.
On one level with cyber criminals: Live Hacking in the Social Network!
Social networks are the “thing” of youth. Even though Facebook is already several years old and has the largest growth in the 50+ generation, valuable personal information can still be found there. But professional networks are also increasingly popular platforms that are used to find the next job. The extensive privacy settings of modern networks do not only affect the company you work for - cyber criminals also find it interesting. But even WhatsApp is already considered a social, closed network and used by criminals because of its popularity for various scams. The story functionality of the Messenger contributes to this. But in all mentioned there are different ways for criminals to achieve their goals. We show this interaction regularly in Live Hacking Shows. 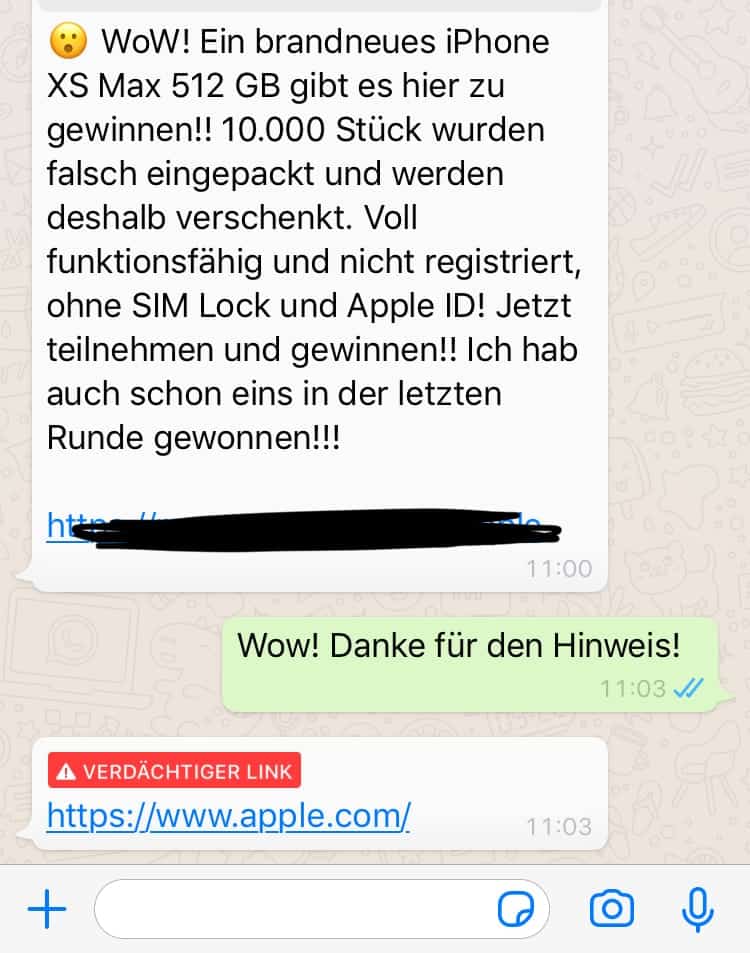
Live Hacking Beispiel für eine bekannte Betrugsmasche (Quelle: Eigene)
If the cyber criminal calls: Call ID spoofing!
Call ID Spoofing is very successful in fraud scams and accordingly popular. Here the sender telephone number of the caller is forged. For this purpose, trustworthy authorities such as the police are misused. We show how criminals implement this scam and how you can protect yourself from this perfidious fraud - protective measures apply equally in private and professional contexts.
Drones Hacking, SMS Spoofing and professional Phishing Mails
There are sufficient examples of successful live hacking. However, the challenge for a successful event depends on many aspects. A good presentation and a reliable internet connection already contribute a large part to this. The rest is taken care of by our Live Hacking speakers - the keynote speakers of the computer science department! https://www.youtube.com/watch?v=lBko95-SxJo
Next Step
Our certified security experts will advise you on the topics covered in this article — free and without obligation.
Free · 30 minutes · No obligation
