
TL;DR
Email encryption uses asymmetric (public key) cryptography: a sender encrypts with the recipient's public key, and only the recipient's private key can decrypt it. The two main standards are S/MIME (used mainly by organizations, keys issued by authorities, supported natively in many mail clients) and OpenPGP (open source via GNuPG, self-managed keys, more suitable for private use). The two are incompatible. The BSI's EasyGPG project aims to simplify GPG adoption by automating key creation and distribution through existing email providers.
Table of Contents (3 sections)
Unfortunately, encryption of emails is used far too little, although it has long been known that emails can be intercepted by third parties on their way to their recipients. The reason why asymmetric encryption is so little used for emails may be that setting up such procedures is usually complicated and thus a deterrent. The most popular protocols for email encryption are S/MIME and OpenPGP.
What is asymmetric encryption?
Asymmetric encryption is a method which is also known as public key method. Each communication partner has a pair of keys, a public key and a private key. When person A wants to send an encrypted message to person B, person A uses person B’s public key to encrypt the message. Person B can then use the private key to decrypt the message again. The public key, which is accessible to everyone, therefore only has a one-way function: you can use it to encrypt messages, but not to decrypt them. 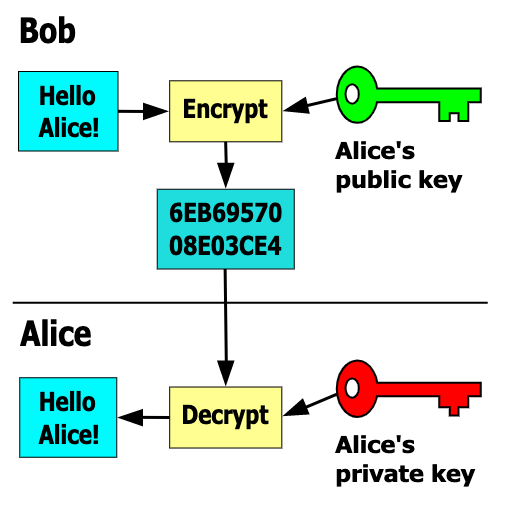
Bob encrypts his message with Alice’s public key. This can in turn decrypt the message with your private key. The basis for asymmetric encryption is also referred to as trapdoor functions, functions that are easy to compute but impossible to invert without a secret (the trapdoor). The public key is thus the description of the function, the private key of the trapdoor.
S/MIME and OpenPGP in comparison
S/MIME stands for Secure/Multipurpose Internet Mail Extensions and, like OpenPGP (Open Pretty Good Privacy), is a standard for encrypting and signing emails using public key methods. However, the two protocols are not compatible with each other, since they use different data formats for partially identical encryption methods. S/MIME has been around since 1995 and is implemented out of the box in many mail programs. With this protocol, however, the two key pairs are not created and distributed by the users themselves, but usually by organizations and companies for a fee. That is why S/MIME is mainly used by companies. OpenPGP (1998), on the other hand, with its open source software GNuPG(GNU Privacy Guard), is more suitable for private use, since all keys can be generated and managed by the user. A commercial alternative to GNuPG would be PGP, on which the OpenPGP standard is based. So S/MIME and OpenPGP both do the same job, and while there are a few important differences, ultimately neither standard offers an overall advantage over the other.
Email encryption - EasyGPG as an alternative?
However, since the installation and setup of such services is usually cumbersome and therefore avoided, the German Federal Office for Information Security (BSI) has launched the EasyGPG project. This is intended to simplify the use of effective email encryption by automating the creation and distribution of the public key to a large extent via the existing email provider. For EasyGPG the necessary mechanisms are provided by GNuPG. The BSI itself has written an article about this, in which EasyGPG is presented again in more detail. Especially emails with sensitive data should be encrypted to prevent a man-in-the-middle attack, where a third party intercepts, reads and possibly manipulates the mail. Such an attack, by the way, is also one of the OWASP Top 10, which was reported in a blog article last week.
Next Step
Our certified security experts will advise you on the topics covered in this article — free and without obligation.
Free · 30 minutes · No obligation
